
Built for blue teams.
Powered by real malware techniques.
Combat Theater is a malware technique testing framework designed specifically for blue team detection engineers and security researchers.
It bridges the gap between blue teaming and malware development by giving defenders the ability to execute real-world malware techniques in isolation - safely, repeatably, and with full visibility.
No weaponised malware. No lab overhead. No infrastructure. Just accurate technique execution that behaves like the real thing.
Detection Engineers
Execute malware techniques, generate telemetry, validate detections effortlessly.
Security Researchers
Experiment with advanced and niche tradecraft without hours of tedious development.
A versatile utility for defenders.
Combat Theater is designed to support a wide range of defensive, research, and validation workflows.
- Control validation and detection coverage testing
- SIEM and EDR regression testing
- Threat emulation and purple teaming
- AV and EDR bypass experimentation
- SOC analyst training utility
- Baseline signal noise and false positive analysis
- Independent product evaluations
- MITRE and Forrester assessment readiness
- IOC generation and validation
- Internal assessments and red team preparation
Everything you need for emulation.
A complete ecosystem for malware technique execution and validation.
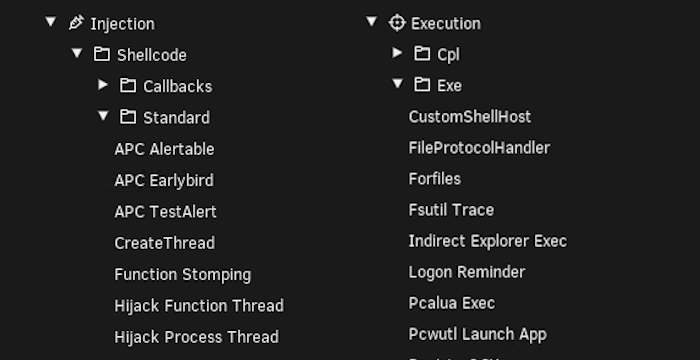
Large Technique Library
Access to one of the largest collections of "ready to execute" malware techniques. From common commodity malware behavior to advanced nation-state tradecraft, our library is constantly updated to reflect the current threat landscape.
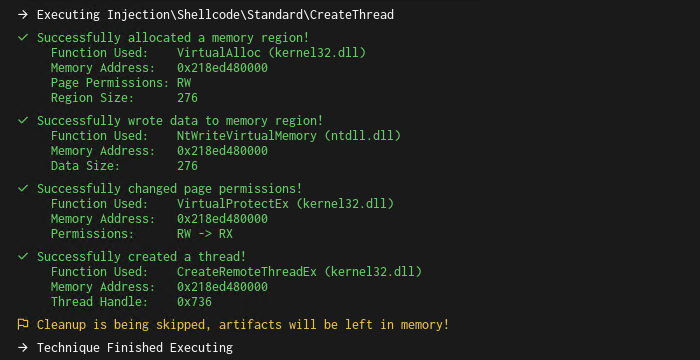
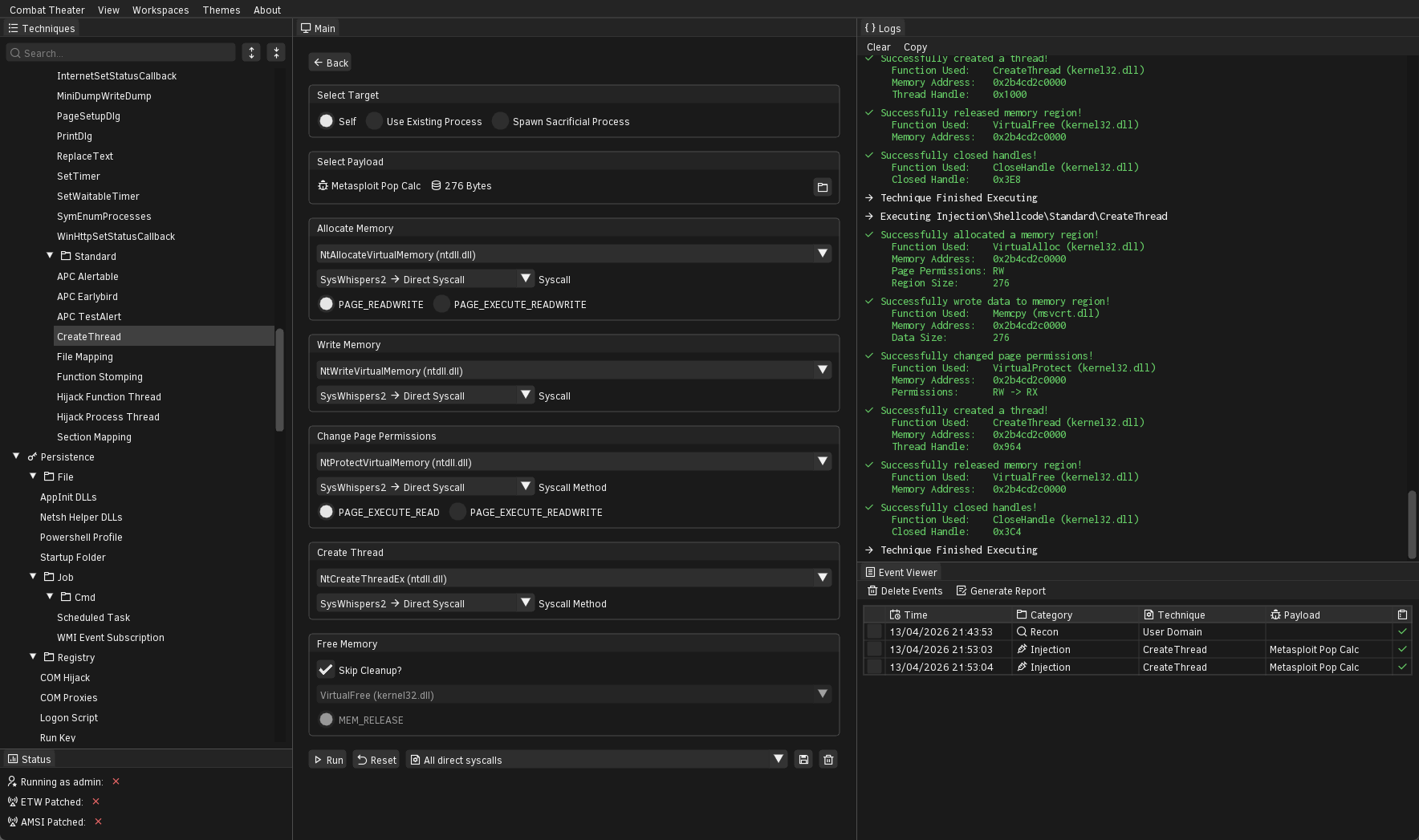
Advanced Logging
Detailed execution logs capture every API call, memory allocation, and system interaction. Validate your telemetry sources with ground-truth data generated directly from the execution engine.
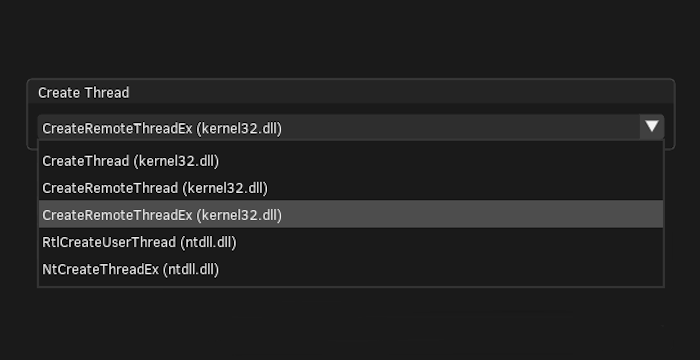
Execution Customization
Choosing a technique to run is just the start. Customize which APIs it will use, which page permissions will be set, all in a no-code pick'n'mix style gui.
Technique Transparency
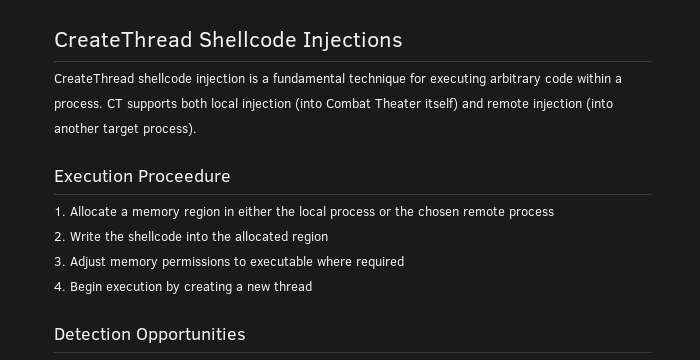
Every technique includes a detailed breakdown of how it works under the hood, from execution flow to the underlying system interactions. It also provides clear detection opportunities helping guide defenders.
Run-safe payloads.
Execute continuously with confidence. Combat Theater uses custom built payloads designed to mimic real malware structure without the malicious side effects.
10+ Supported Types
From raw shellcode and DLLs to EXEs and more exotic formats. We provide a wide range of payload types out of the box.
Peace of Mind
Our "run safe" payloads perform no network connections and no destructive actions.
Authentic Architecture
Though benign, payloads are compiled with realistic headers, sections, and entry points to trigger behavioral analysis correctly.
Bring Your Own
Easily import your own real-world samples or custom developed payloads. The framework is agnostic to what you execute.

Chain techniques into playbooks.
Playbooks let you sequence multiple techniques into a single execution flow. Build your own with our playbook builder or choose from a number of our pre curated ones, all executable in just one click.
APT
Emulate known nation-state tradecraft and advanced persistent threat chains.
Criminal
Reproduce ransomware group activity and commodity malware behaviour.
Espionage
Simulate reconnaissance, credential harvesting, and covert data exfiltration.
Challenge
Curated detection challenges — from easy wins to obscure, hard-to-catch techniques.
Implement your own techniques with Lua.
We provide 120+ ready to go technique scripts, however should you want to add your own or customize existing techniques, we expose our custom "ctapi" for you.
Combat Theater uses Lua as a control and orchestration layer, while all technique execution is performed by a native C++ engine.
Lua defines the GUI, configuration, and execution flow of a technique, but the underlying behavior is handled entirely by C++. This ensures techniques behave like real malware but with the ease of scripting.
-- CreateRemoteThread Shellcode Injection
local meta = require "meta"
local gui = require "gui"
local api = require "api"
function Init()
meta.SetRequiredPermissions("user")
meta.SetSupportedPayloads("shellcode")
meta.SetReadme(readme)
end
function Configurator()
gui.SetTarget(ctxTarget, true, true, true, false)
gui.SetPayload(ctxPayload);
gui.AllocateMemory(ctxAlloc)
gui.WriteMemory(ctxWrite)
gui.ChangePagePermissions(ctxPage)
gui.CreateThread(ctxThread)
gui.FreeMemory(ctxFree)
end
function ExecuteTechnique()
-- Init
local hTargetProcess, hTargetThread = api.InitializeTarget(ctxTarget)
-- Payload
local pPayload, iPayloadSize = api.GetPayload(ctxPayload)
-- Memory
local pPayloadAddress = api.AllocateMemory(ctxAlloc, hTargetProcess, iPayloadSize)
api.WriteMemory(ctxWrite, hTargetProcess, pPayloadAddress, pPayload, iPayloadSize)
api.ChangePagePermissions(ctxPage, hTargetProcess, pPayloadAddress, iPayloadSize)
-- Execute
local hThread = api.CreateThread(ctxThread, hTargetProcess, pPayloadAddress, false)
-- Cleanup
api.FreeMemory(ctxFree, hTargetProcess, pPayloadAddress)
api.FreePayload(pPayload)
api.CloseHandles(ctxFree, hTargetProcess, hTargetThread, hThread)
end
Run where it's convenient.
Combat Theater is designed to run in constrained environments without heavy dependencies or specialized hardware.
Supported operating systems
- Windows 10 (64-bit)
- Windows 11 (64-bit)
- Windows Server 2019 / 2022
Runtime environment
- No GPU or graphics drivers required
- Runs in cloud and local virtual machines
- Suitable for low-spec systems
Deployment flexibility
- Local analyst workstations
- Cloud-hosted VMs & Labs
- Automated testing and pipeline hosts
See it in action.
Licensing options.
- All techniques
- Advanced execution logging
- Internal use only
- Event viewer & report generation
- Standard support
- Email notifications
- Floating licenses
- All techniques
- Advanced execution logging
- External use permitted
- Event viewer & report generation
- Headless commandline mode
- Playbook builder & runner
- Priority support
- Email notifications
- Floating licenses
- Team discounts available